My interview with The Register on The International Committee of the Red Cross (ICRC) setting out eight rules for hacktivists to discourage civilian involvement in cyberattacks against other countries.
-

Major Data Breach Exposes Domestic Abuse Victims
My interview on the Vanessa Feltz show on TalkTV about a major data breach which has rocked multiple organizations, including an NHS trust, a police service, a government department, and local councils, resulting in the exposure of the locations of domestic abuse victims to their alleged abusers.
This breach appears to have put the lives of women and children at risk, as their addresses and whereabouts, crucial information for their safety, have fallen into the wrong hands.
-

Apple to Fix iPhone Radiation Levels with Software Update
My interview on BBC Radio Foyle about Apple Fixing iPhone Radiation Levels with Software Update & airplane mode on flights.
-

Ransomware volumes at record high after Clop’s MOVEit attacks
My piece in Global Security Magazine on MOVEit attacks having driven ransomware attacks to a record high, according to NCC Group’s global threat intelligence team.
-
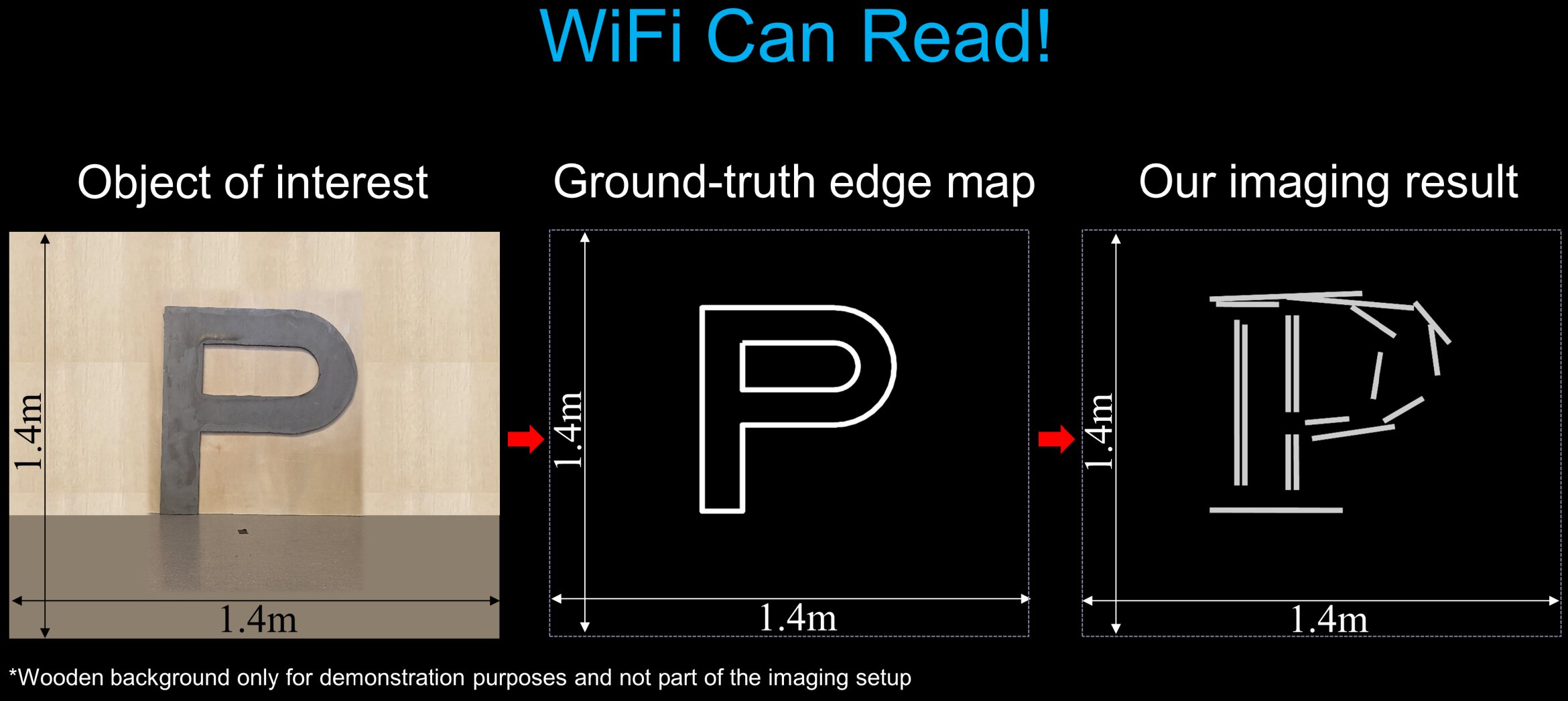
China bans iPhones in Government – WiFi reading & Smart Toilets
My interview on BBC Radio Foyle about the Chinese government banning iPhones for some government workers, WiFi enabled reading & worries over smart toilets being hacked.
-

How can companies adapt their approach to ensure comprehensive protection across their networks
My interview with Intelligent CISO on the risks inherent in poorly deployed IoT devices.
-

Google: Celebrating 25 Years of Revolutionizing Search
My interview on BBC Radio Ulster on the 25th anniversary of Google which is recognised by Forbes as the second most valuable brand on the Planet.
-

Russian cyber-attacks ‘relentless’ as threat of WW3 grows, expert warns
My interview in The Independent on sensitive information about sites including HMNB Clyde, home of the Trident nuclear submarines, and GCHQ, being leaked.
-

Skilled and trained workforce needed to combat cyber risks
My interview in Cyber Magazine on how there needs to be a collective effort from businesses, industry groups, schools and universities to encourage more young people to enter the cybersecurity industry.
-

Met Police probes ‘unauthorised access’ to IT system containing details of police officers
My interview on LBC News about the Metropolitan Police looking into a possible security breach after one of its contractors reported ‘unauthorised access’ on its IT system.

